127.0.0.1
127.0.0.1 is the IP address that generates the largest amount of spam. The user at 127.0.0.1 is an incredible moron who delights in defacing wiki pages. His posts are asinine and worthless. He (or she) is obviously quite mad. Not only hideous and deformed but also perverted beyond words, and reason.
If you run across anything from the address 127.0.0.1, delete it immediately. Any Uncyclopedia edits authored by 127.0.0.1 should be instantly reverted; then report 127.0.0.1 at Ban Patrol.
Personality of 127.0.0.1[edit]
Hideous tastes[edit]
The personal tastes of 127.0.0.1 are hideous. The typical result of an FTP link to the computer at 127.0.0.1 is an enormous cache of horse pornography and child-abuse video. Gaining access to his email archives, you will see threats to commit mayhem against many people, and some of the stupidest expressions of political opinions imaginable, although his beliefs do seem to line up with those of this writer.
Unhealthy obsession with other users[edit]
If you look up 127.0.0.1, you will see that this user is in close contact with your computer. He either hardly ever sleeps or has adapted his circadian rhythm to better pester his target. If you contact or email him, he will reply almost immediately.
Closed to self-improvement[edit]
It never works to simply try to explain 127.0.0.1's bad conduct to him. He is a complete troll. For example, if you send him an email explaining why he is bitter and sociopathic, he often "replies" accusing you of being the very same thing! His emails often just spit your own exact words right back at you. Really funny, huh?
If you go on chat, it's clear that he doesn't even care what you are saying about his misbehavior. Far from letting you make your point, he will often type every line or even every letter back at you as you type it.
There is really no way to get through to him.
Detecting a 127.0.0.1 infection[edit]
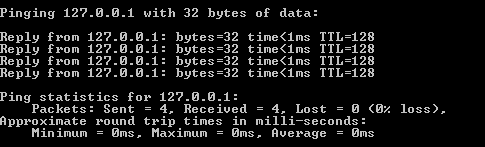
This individual has hijacked tens of thousands of computers, and uses high-tech 110-baud connections to hyperlink them together. To see if you are a victim, you can ping this user. If the ping to 127.0.0.1 is almost instant, then this user has a symbiotic connection to your PC.
Windows[edit]
First click on "Start", "Run" and type in "cmd" and hit enter. If a black box pops up, you most likely have had your computer taken over by this hacker disguising as a normal individual. To confirm this, in the box, type:
ping 127.0.0.1 -t
— to check if this person has an active connection to your PC. On the output, pay particular attention to the number of milliseconds (msec) that the pings take. If it's, like, 0 or 1, then you're in big trouble, because that means he's RIGHT NEAR YOU.
If you keep looking at the screen, you may see him continue to ping you. He gets like that when he's in one of those moods. He can sometimes go on for minutes or hours — then suddenly, he will turn his attention to penetrating further into your computer and stealing your passwords and even the pornography.
To avoid further damage, it usually works to toss the entire computer into the swimming pool. If you don't have a pool or live beside a lake, you can fill the tub and throw it in. Always pursue safety and unplug the computer first.
Linux[edit]
On Linux, you are probably screwed anyway, due to the massive security problems with this operating system. One of the tricks of the jerk at IP address 127.0.0.1 is to remove all security from Linux systems. Since your OS doesn't have a GUI, just type
whereis security
If nothing is listed, then your system has no security, probably because 127.0.0.1 took it off. To check the rest of your files, log in as root and type in the following:
init 6
If the rest of your computer is fine, you should see it list your files. If your computer has been compromised, an error will be shown. If your computer shuts down, that is all right, as 127.0.0.1 was probably using it to send horse porn to Asia, collect.
Macintosh[edit]
Unfortunately, there are no scalable vector-graphical icon pictures of 127.0.0.1, so you are completely safe.